We use cookies, including cookies from third parties, to enhance your user experience and the effectiveness of our marketing activities. These cookies are performance, analytics and advertising cookies, please see our Privacy and Cookie policy for further information. If you agree to all of our cookies select “Accept all” or select “Cookie Settings” to see which cookies we use and choose which ones you would like to accept.
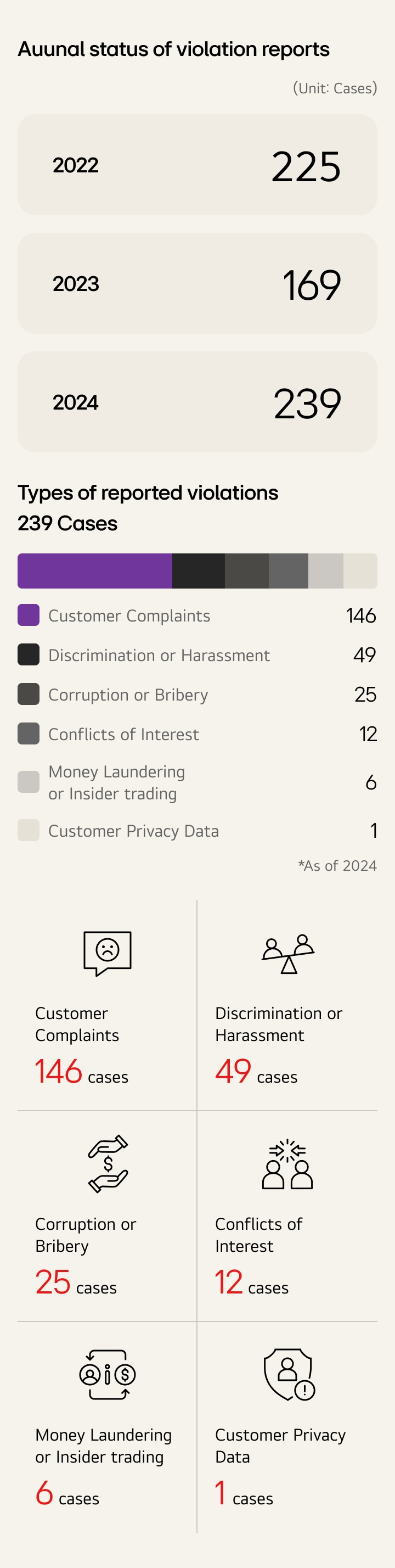
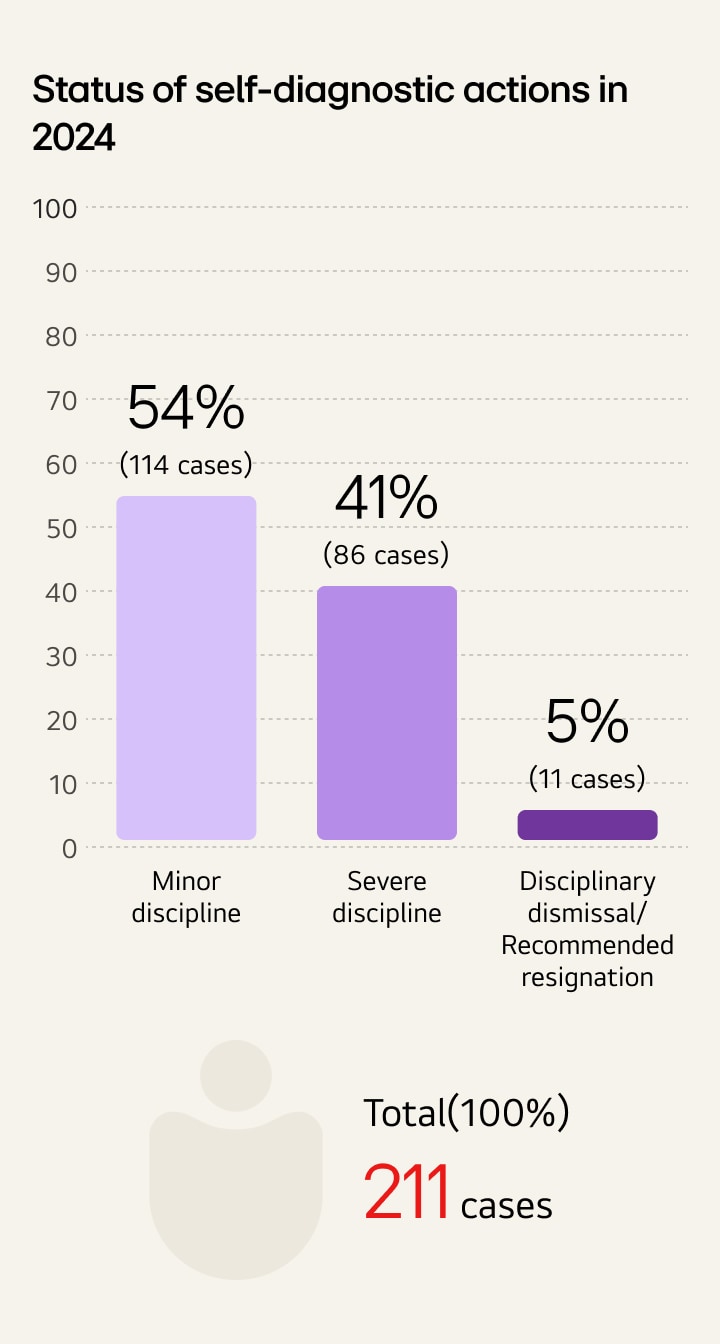
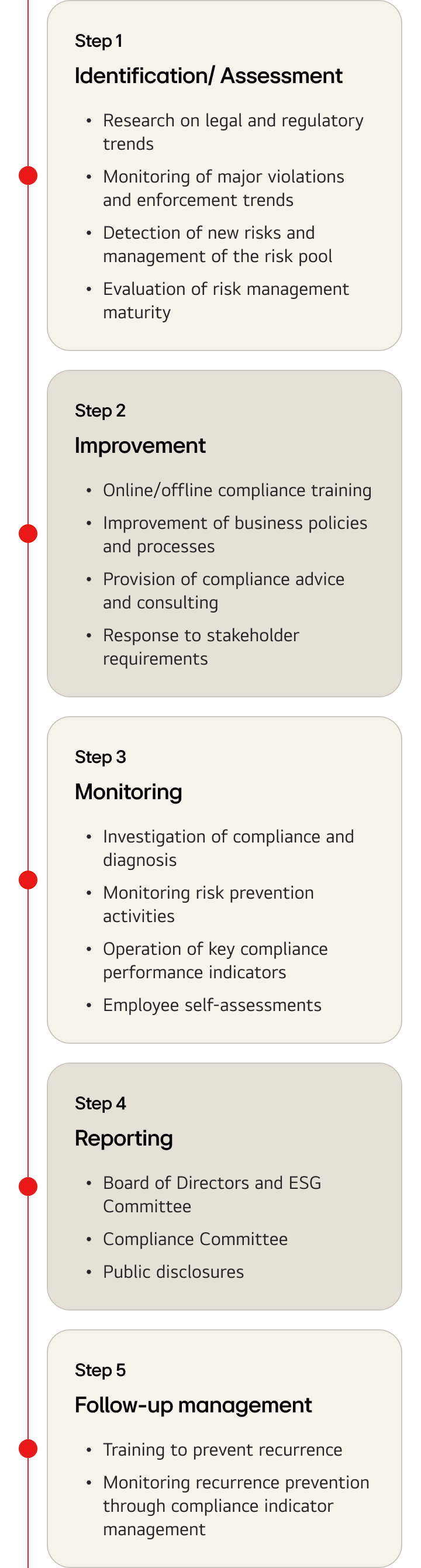
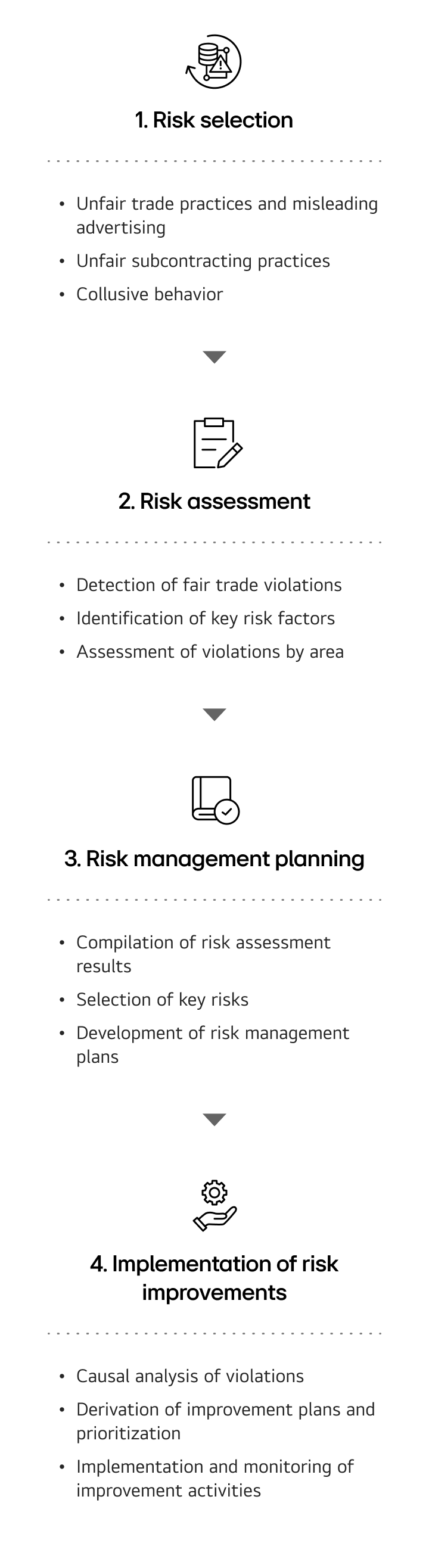
Building trust through responsible leadership
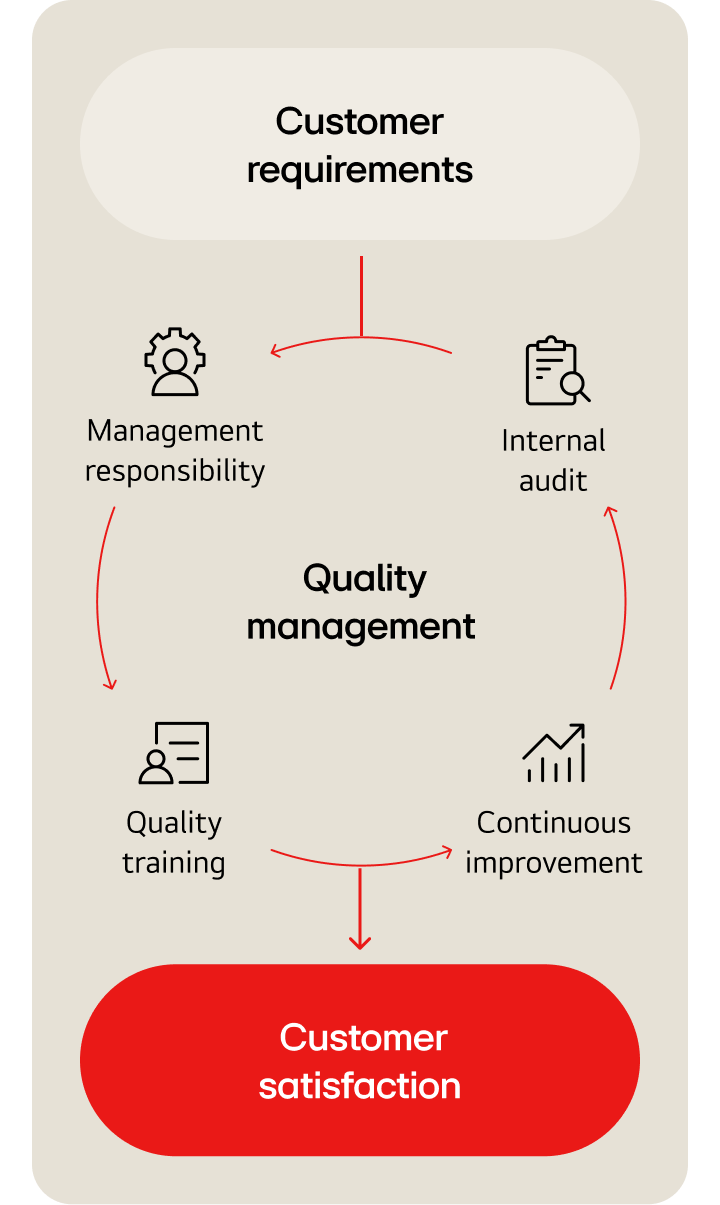
Guided by 'creating value for customers' and 'respecting people', LG Electronics applies 'Jeong-Do Management' and ethics to foster a sound culture and practice trusted responsible management.